 |
| September 17, 2013 | Volume 09 Issue 35 |
Electrical/Electronic News & Products
Designfax weekly eMagazine
Archives
Partners
Manufacturing Center
Product Spotlight
Modern Applications News
Metalworking Ideas For
Today's Job Shops
Tooling and Production
Strategies for large
metalworking plants
Intro to reed switches, magnets, magnetic fields
 This brief introductory video on the DigiKey site offers tips for engineers designing with reed switches. Dr. Stephen Day, Ph.D. from Coto Technology gives a solid overview on reed switches -- complete with real-world application examples -- and a detailed explanation of how they react to magnetic fields.
This brief introductory video on the DigiKey site offers tips for engineers designing with reed switches. Dr. Stephen Day, Ph.D. from Coto Technology gives a solid overview on reed switches -- complete with real-world application examples -- and a detailed explanation of how they react to magnetic fields.
View the video.
Bi-color LEDs to light up your designs
 Created with engineers and OEMs in mind, SpectraBright Series SMD RGB and Bi-Color LEDs from Visual Communi-cations Company (VCC) deliver efficiency, design flexibility, and control for devices in a range of industries, including mil-aero, automated guided vehicles, EV charging stations, industrial, telecom, IoT/smart home, and medical. These 50,000-hr bi-color and RGB options save money and space on the HMI, communicating two or three operating modes in a single component.
Created with engineers and OEMs in mind, SpectraBright Series SMD RGB and Bi-Color LEDs from Visual Communi-cations Company (VCC) deliver efficiency, design flexibility, and control for devices in a range of industries, including mil-aero, automated guided vehicles, EV charging stations, industrial, telecom, IoT/smart home, and medical. These 50,000-hr bi-color and RGB options save money and space on the HMI, communicating two or three operating modes in a single component.
Learn more.
All about slip rings: How they work and their uses
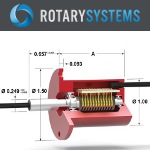 Rotary Systems has put together a really nice basic primer on slip rings -- electrical collectors that carry a current from a stationary wire into a rotating device. Common uses are for power, proximity switches, strain gauges, video, and Ethernet signal transmission. This introduction also covers how to specify, assembly types, and interface requirements. Rotary Systems also manufactures rotary unions for fluid applications.
Rotary Systems has put together a really nice basic primer on slip rings -- electrical collectors that carry a current from a stationary wire into a rotating device. Common uses are for power, proximity switches, strain gauges, video, and Ethernet signal transmission. This introduction also covers how to specify, assembly types, and interface requirements. Rotary Systems also manufactures rotary unions for fluid applications.
Read the overview.
Seifert thermoelectric coolers from AutomationDirect
 Automation-Direct has added new high-quality and efficient stainless steel Seifert 340 BTU/H thermoelectric coolers with 120-V and 230-V power options. Thermoelectric coolers from Seifert use the Peltier Effect to create a temperature difference between the internal and ambient heat sinks, making internal air cooler while dissipating heat into the external environment. Fans assist the convective heat transfer from the heat sinks, which are optimized for maximum flow.
Automation-Direct has added new high-quality and efficient stainless steel Seifert 340 BTU/H thermoelectric coolers with 120-V and 230-V power options. Thermoelectric coolers from Seifert use the Peltier Effect to create a temperature difference between the internal and ambient heat sinks, making internal air cooler while dissipating heat into the external environment. Fans assist the convective heat transfer from the heat sinks, which are optimized for maximum flow.
Learn more.
EMI shielding honeycomb air vent panel design
 Learn from the engineering experts at Parker how honeycomb air vent panels are used to help cool electronics with airflow while maintaining electromagnetic interference (EMI) shielding. Topics include: design features, cell size and thickness, platings and coatings, and a stacked design called OMNI CELL construction. These vents can be incorporated into enclosures where EMI radiation and susceptibility is a concern or where heat dissipation is necessary. Lots of good info.
Learn from the engineering experts at Parker how honeycomb air vent panels are used to help cool electronics with airflow while maintaining electromagnetic interference (EMI) shielding. Topics include: design features, cell size and thickness, platings and coatings, and a stacked design called OMNI CELL construction. These vents can be incorporated into enclosures where EMI radiation and susceptibility is a concern or where heat dissipation is necessary. Lots of good info.
Read the Parker blog.
What is 3D-MID? Molded parts with integrated electronics from HARTING
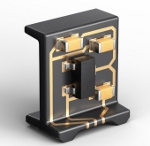 3D-MID (three-dimensional mechatronic integrated devices) technology combines electronic and mechanical functionalities into a single, 3D component. It replaces the traditional printed circuit board and opens up many new opportunities. It takes injection-molded parts and uses laser-direct structuring to etch areas of conductor structures, which are filled with a copper plating process to create very precise electronic circuits. HARTING, the technology's developer, says it's "Like a PCB, but 3D." Tons of possibilities.
3D-MID (three-dimensional mechatronic integrated devices) technology combines electronic and mechanical functionalities into a single, 3D component. It replaces the traditional printed circuit board and opens up many new opportunities. It takes injection-molded parts and uses laser-direct structuring to etch areas of conductor structures, which are filled with a copper plating process to create very precise electronic circuits. HARTING, the technology's developer, says it's "Like a PCB, but 3D." Tons of possibilities.
View the video.
Loss-free conversion of 3D/CAD data
 CT CoreTech-nologie has further developed its state-of-the-art CAD converter 3D_Evolution and is now introducing native interfaces for reading Solidedge and writing Nx and Solidworks files. It supports a wide range of formats such as Catia, Nx, Creo, Solidworks, Solidedge, Inventor, Step, and Jt, facilitating smooth interoperability between different systems and collaboration for engineers and designers in development environments with different CAD systems.
CT CoreTech-nologie has further developed its state-of-the-art CAD converter 3D_Evolution and is now introducing native interfaces for reading Solidedge and writing Nx and Solidworks files. It supports a wide range of formats such as Catia, Nx, Creo, Solidworks, Solidedge, Inventor, Step, and Jt, facilitating smooth interoperability between different systems and collaboration for engineers and designers in development environments with different CAD systems.
Learn more.
Top 5 reasons for solder joint failure
 Solder joint reliability is often a pain point in the design of an electronic system. According to Tyler Ferris at ANSYS, a wide variety of factors affect joint reliability, and any one of them can drastically reduce joint lifetime. Properly identifying and mitigating potential causes during the design and manufacturing process can prevent costly and difficult-to-solve problems later in a product lifecycle.
Solder joint reliability is often a pain point in the design of an electronic system. According to Tyler Ferris at ANSYS, a wide variety of factors affect joint reliability, and any one of them can drastically reduce joint lifetime. Properly identifying and mitigating potential causes during the design and manufacturing process can prevent costly and difficult-to-solve problems later in a product lifecycle.
Read this informative ANSYS blog.
Advanced overtemp detection for EV battery packs
 Littelfuse has introduced TTape, a ground-breaking over-temperature detection platform designed to transform the management of Li-ion battery systems. TTape helps vehicle systems monitor and manage premature cell aging effectively while reducing the risks associated with thermal runaway incidents. This solution is ideally suited for a wide range of applications, including automotive EV/HEVs, commercial vehicles, and energy storage systems.
Littelfuse has introduced TTape, a ground-breaking over-temperature detection platform designed to transform the management of Li-ion battery systems. TTape helps vehicle systems monitor and manage premature cell aging effectively while reducing the risks associated with thermal runaway incidents. This solution is ideally suited for a wide range of applications, including automotive EV/HEVs, commercial vehicles, and energy storage systems.
Learn more.
Benchtop ionizer for hands-free static elimination
 EXAIR's Varistat Benchtop Ionizer is the latest solution for neutralizing static on charged surfaces in industrial settings. Using ionizing technology, the Varistat provides a hands-free solution that requires no compressed air. Easily mounted on benchtops or machines, it is manually adjustable and perfect for processes needing comprehensive coverage such as part assembly, web cleaning, printing, and more.
EXAIR's Varistat Benchtop Ionizer is the latest solution for neutralizing static on charged surfaces in industrial settings. Using ionizing technology, the Varistat provides a hands-free solution that requires no compressed air. Easily mounted on benchtops or machines, it is manually adjustable and perfect for processes needing comprehensive coverage such as part assembly, web cleaning, printing, and more.
Learn more.
LED light bars from AutomationDirect
 Automation-Direct adds CCEA TRACK-ALPHA-PRO series LED light bars to expand their offering of industrial LED fixtures. Their rugged industrial-grade anodized aluminum construction makes TRACKALPHA-PRO ideal for use with medium to large-size industrial machine tools and for use in wet environments. These 120 VAC-rated, high-power LED lights provide intense, uniform lighting, with up to a 4,600-lumen output (100 lumens per watt). They come with a standard bracket mount that allows for angle adjustments. Optional TACLIP mounts (sold separately) provide for extra sturdy, vibration-resistant installations.
Automation-Direct adds CCEA TRACK-ALPHA-PRO series LED light bars to expand their offering of industrial LED fixtures. Their rugged industrial-grade anodized aluminum construction makes TRACKALPHA-PRO ideal for use with medium to large-size industrial machine tools and for use in wet environments. These 120 VAC-rated, high-power LED lights provide intense, uniform lighting, with up to a 4,600-lumen output (100 lumens per watt). They come with a standard bracket mount that allows for angle adjustments. Optional TACLIP mounts (sold separately) provide for extra sturdy, vibration-resistant installations.
Learn more.
World's first metalens fisheye camera
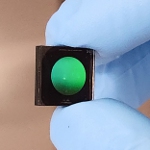 2Pi Optics has begun commercial-ization of the first fisheye camera based on the company's proprietary metalens technology -- a breakthrough for electronics design engineers and product managers striving to miniaturize the tiny digital cameras used in advanced driver-assistance systems (ADAS), AR/VR, UAVs, robotics, and other industrial applications. This camera can operate at different wavelengths -- from visible, to near IR, to longer IR -- and is claimed to "outperform conventional refractive, wide-FOV optics in all areas: size, weight, performance, and cost."
2Pi Optics has begun commercial-ization of the first fisheye camera based on the company's proprietary metalens technology -- a breakthrough for electronics design engineers and product managers striving to miniaturize the tiny digital cameras used in advanced driver-assistance systems (ADAS), AR/VR, UAVs, robotics, and other industrial applications. This camera can operate at different wavelengths -- from visible, to near IR, to longer IR -- and is claimed to "outperform conventional refractive, wide-FOV optics in all areas: size, weight, performance, and cost."
Learn more.
Orbex offers two fiber optic rotary joint solutions
 Orbex Group announces its 700 Series of fiber optic rotary joint (FORJ) assemblies, supporting either single or multi-mode operation ideal for high-speed digital transmission over long distances. Wavelengths available are 1,310 or 1,550 nm. Applications include marine cable reels, wind turbines, robotics, and high-def video transmission. Both options feature an outer diameter of 7 mm for installation in tight spaces. Construction includes a stainless steel housing.
Orbex Group announces its 700 Series of fiber optic rotary joint (FORJ) assemblies, supporting either single or multi-mode operation ideal for high-speed digital transmission over long distances. Wavelengths available are 1,310 or 1,550 nm. Applications include marine cable reels, wind turbines, robotics, and high-def video transmission. Both options feature an outer diameter of 7 mm for installation in tight spaces. Construction includes a stainless steel housing.
Learn more.
Mini tunnel magneto-resistance effect sensors
 Littelfuse has released its highly anticipated 54100 and 54140 mini Tunnel Magneto-Resistance (TMR) effect sensors, offering unmatched sensitivity and power efficiency. The key differentiator is their remarkable sensitivity and 100x improvement in power efficiency compared to Hall Effect sensors. They are well suited for applications in position and limit sensing, RPM measurement, brushless DC motor commutation, and more in various markets including appliances, home and building automation, and the industrial sectors.
Littelfuse has released its highly anticipated 54100 and 54140 mini Tunnel Magneto-Resistance (TMR) effect sensors, offering unmatched sensitivity and power efficiency. The key differentiator is their remarkable sensitivity and 100x improvement in power efficiency compared to Hall Effect sensors. They are well suited for applications in position and limit sensing, RPM measurement, brushless DC motor commutation, and more in various markets including appliances, home and building automation, and the industrial sectors.
Learn more.
Panasonic solar and EV components available from Newark
 Newark has added Panasonic Industry's solar inverters and EV charging system components to their power portfolio. These best-in-class products help designers meet the growing global demand for sustainable and renewable energy mobility systems. Offerings include film capacitors, power inductors, anti-surge thick film chip resistors, graphite thermal interface materials, power relays, capacitors, and wireless modules.
Newark has added Panasonic Industry's solar inverters and EV charging system components to their power portfolio. These best-in-class products help designers meet the growing global demand for sustainable and renewable energy mobility systems. Offerings include film capacitors, power inductors, anti-surge thick film chip resistors, graphite thermal interface materials, power relays, capacitors, and wireless modules.
Learn more.
Encryption is less secure than we thought
For 65 years, most information-theoretic analyses of cryptographic systems have made a mathematical assumption that turns out to be wrong.
By Larry Hardesty, MIT
Information theory -- the discipline that gave us digital communication and data compression -- also put cryptography on a secure mathematical foundation. Since 1948, when the paper that created information theory first appeared, most information-theoretic analyses of secure schemes have depended on a common assumption.
Unfortunately, as a group of researchers at MIT and the National University of Ireland (NUI) at Maynooth demonstrated in a paper presented at the recent International Symposium on Information Theory (view PDF), that assumption is false. In a follow-up paper being presented this fall at the Asilomar Conference on Signals and Systems, the same team shows that, as a consequence, the wireless card readers used in many keyless-entry systems may not be as secure as previously thought.
In information theory, the concept of information is intimately entwined with that of entropy. Two digital files might contain the same amount of information, but if one is shorter, it has more entropy. If a compression algorithm -- such as WinZip or gzip -- worked perfectly, the compressed file would have the maximum possible entropy. That means that it would have the same number of 0s and 1s, and the way in which they were distributed would be totally unpredictable. In information-theoretic parlance, it would be perfectly uniform.
Traditionally, information-theoretic analyses of secure schemes have assumed that the source files are perfectly uniform. In practice, they rarely are, but they're close enough that it appeared that the standard mathematical analyses still held.
"We thought we'd establish that the basic premise that everyone was using was fair and reasonable," says Ken Duffy, one of the researchers at NUI. "And it turns out that it's not." On both papers, Duffy is joined by his student Mark Christiansen; Muriel Medard, a professor of electrical engineering at MIT; and her student Flavio du Pin Calmon.
The problem, Medard explains, is that information-theoretic analyses of secure systems have generally used the wrong notion of entropy. They relied on so-called Shannon entropy, named after the founder of information theory, Claude Shannon, who taught at MIT from 1956 to 1978.
Shannon entropy is based on the average probability that a given string of bits will occur in a particular type of digital file. In a general-purpose communications system, that's the right type of entropy to use, because the characteristics of the data traffic will quickly converge to the statistical averages. Although Shannon's seminal 1948 paper dealt with cryptography, it was primarily concerned with communication, and it used the same measure of entropy in both discussions.
But in cryptography, the real concern isn't with the average case but with the worst case. A codebreaker needs only one reliable correlation between the encrypted and unencrypted versions of a file in order to begin to deduce further correlations. In the years since Shannon's paper, information theorists have developed other notions of entropy, some of which give greater weight to improbable outcomes. Those, it turns out, offer a more accurate picture of the problem of codebreaking.
When Medard, Duffy, and their students used these alternate measures of entropy, they found that slight deviations from perfect uniformity in source files, which seemed trivial in the light of Shannon entropy, suddenly loomed much larger. The upshot is that a computer turned loose to simply guess correlations between the encrypted and unencrypted versions of a file would make headway much faster than previously expected.
"It's still exponentially hard, but it's exponentially easier than we thought," Duffy says. One implication is that an attacker who simply relied on the frequencies with which letters occur in English words could probably guess a user-selected password much more quickly than was previously thought. "Attackers often use graphics processors to distribute the problem," Duffy says. "You'd be surprised at how quickly you can guess stuff."
In their Asilomar paper, the researchers apply the same type of mathematical analysis in a slightly different way. They consider the case in which an attacker is, from a distance, able to make a "noisy" measurement of the password stored on a credit card with an embedded chip or a key card used in a keyless-entry system.
"Noise" is the engineer's term for anything that degrades an electromagnetic signal -- such as physical obstructions, out-of-phase reflections, or other electromagnetic interference. Noise comes in lots of different varieties: The familiar white noise of sleep aids is one, but so is pink noise, black noise, and more exotic-sounding types of noise, such as power-law noise or Poisson noise.
In this case, rather than prior knowledge about the statistical frequency of the symbols used in a password, the attacker has prior knowledge about the probable noise characteristics of the environment: Phase noise with one set of parameters is more probable than phase noise with another set of parameters, which in turn is more probable than Brownian noise, and so on. Armed with these statistics, an attacker could infer the password stored on the card much more rapidly than was previously thought.
Published September 2013
Rate this article
View our terms of use and privacy policy
